The .de domain outage matters because one DNSSEC mistake can break a country-scale namespace
The recent .de disruption was not a normal website outage. It was a DNSSEC trust-chain failure at registry level, and that makes the lessons much bigger than one bad evening for German domains.
The most important thing about the recent .de domain disruption is not that websites went down for a few hours. It is that a failure in a core trust mechanism made a huge national domain space look broken even when many affected services themselves were technically fine.
That is what makes this outage more interesting than an ordinary hosting problem. The issue did not sit at the edge. It sat near the center of trust: the DNSSEC signing chain for the .de zone.
What is confirmed so far
Heise reconstructs the incident in unusual technical detail and DENIC has confirmed the broad outline publicly.
The confirmed points are:
- the disruption affected .de domains on the evening of May 5, 2026
- the problem was linked to faulty DNSSEC signatures
- the outage disproportionately affected users behind validating resolvers
- DENIC later rolled back to a stable state and restored normal operation
- the event was temporally and logically linked to a routine key rotation
DENIC’s update says the incident began around 21:57, corrected zone distribution started at 00:08, and the previous stable operating state was fully restored by 01:15.
Why DNSSEC turned a signing problem into a reachability problem
This is the key point non-DNS people usually miss.
DNSSEC is designed to make DNS answers trustworthy by validating a signed chain from the root down through the top-level domain and onward. If one part of that chain is broken, validating resolvers do exactly what they are supposed to do: they reject the response.
That is good for security in normal conditions. It is terrible for availability when the signature itself is wrong.
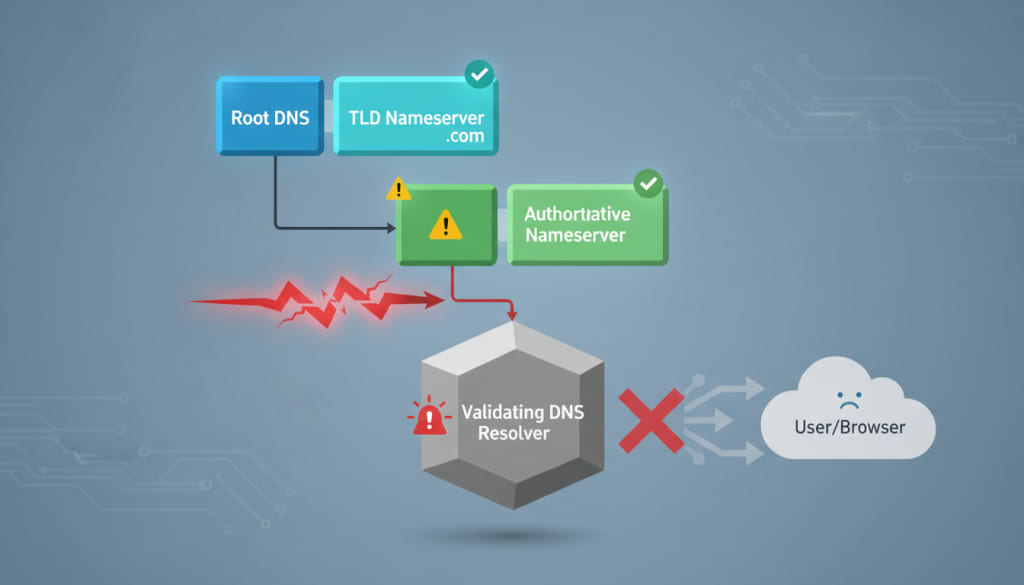
In practical terms, that means users can see websites fail, apps break, and VPN connections die — not because the target system is down, but because its domain resolution is no longer trusted.
What Heise’s reconstruction adds
Heise goes further than the short official note and reconstructs the key timeline using historical DNS data from DNSViz.
According to that analysis:
- a new public key with the ID 33834 was introduced on May 2
- the new key first appeared as a signing key for the zone’s SOA record on May 5 at 21:43 UTC+2
- that signature was invalid
- all six authoritative nameservers served the bad signature at that moment
- operators then entered a chaotic recovery phase, with different servers temporarily serving different combinations of valid and invalid signatures
- the key rollover was ultimately reversed and the zone stabilized again using the older key 32911
That matters because it shows this was not a generic outage with an unknown cause. It appears tied to a specific DNSSEC rollover sequence that went wrong in a live registry environment.
Why only some users were affected more than others
DENIC’s statement highlights an important nuance: not all users were hit equally.
The strongest failures happened where the DNS path relied on DNSSEC-validating resolvers. Those resolvers rejected the broken records entirely. Some resolver operators temporarily suspended validation for .de as a workaround.
This is why the outage looked inconsistent from the outside. Some people saw hard failures, some saw partial recovery, and some recovered faster than others depending on where and how resolution was handled.
Why this outage matters beyond Germany
The .de namespace is one of the world’s most important country-code top-level domains. When something breaks there, the lesson is not local.
This incident matters internationally because it illustrates a broader truth about internet infrastructure:
| Layer | Why it matters |
|---|---|
| DNSSEC | improves integrity and trust in DNS responses |
| key rotation | is routine, but operationally sensitive |
| registry operations | can become a single point of failure at enormous scale |
| resolver behavior | determines how sharply the outage is felt by end users |

Heise also notes that similar DNSSEC-related incidents have happened in other ccTLD contexts before, including .se and .ru, though the mechanics were different. That makes this less of a one-off anomaly and more of a reminder that DNSSEC correctness is unforgiving.
The harder question DENIC now has to answer
The immediate outage is over. The more important issue now is operational confidence.
DENIC has already said future key changes are paused until the exact technical cause is identified. That is the right first move. But the questions that matter next are sharper:
- why did the invalid signatures get generated in the first place?
- why were they distributed across all authoritative servers?
- why did testing or preflight validation not catch the failure before rollout?
- what changes will prevent a repeat during the next rollover?
This was a cryptographic maintenance event gone wrong, and rollback plus pause is the right short-term stability response.
From the outside, a national namespace failed in a way most domain operators could not control, which is why transparency matters almost as much as repair.
Final verdict
The .de outage is a useful reminder that internet reliability is often constrained by trust infrastructure, not just server uptime.
A broken DNSSEC chain can turn a healthy service into an unreachable one at enormous scale, and that is exactly what makes this incident important. Heise’s deeper reconstruction suggests the issue was not vague “technical trouble,” but a concrete failure around DNSSEC key rollover and signature validity. DENIC has restored service, but the more lasting story is the one infrastructure operators everywhere will care about: how routine cryptographic hygiene can become a national outage when the trust chain breaks at the top.
Based on current reporting and DENIC’s public statement, the incident was linked to faulty DNSSEC signatures during a key rotation process.
